March, 29 2016, 06:30pm EDT

If the FBI Doesn't Tell Apple How They Hacked the San Bernardino iPhone, They're Putting Lives at Risk
Following public outcry about the dangers of government-mandated backdoors, the FBI backed down and opened the San Bernardino shooter's iPhone without Apple's help. If they really care about public safety, they must disclose the vulnerability they used to Apple to prevent criminals, hackers, and terrorists from exploiting the same security flaw and using it to do harm.
Following public outcry about the dangers of government-mandated backdoors, the FBI backed down and opened the San Bernardino shooter's iPhone without Apple's help. If they really care about public safety, they must disclose the vulnerability they used to Apple to prevent criminals, hackers, and terrorists from exploiting the same security flaw and using it to do harm.
Encryption protects our hospitals, airports, power plants, and water treatment facilities. Sensitive information about critical infrastructure is stored on phones, computers, and in the cloud. The only thing preventing it from falling into the wrong hands is strong security technology.
Security experts agree that when a government agency discovers a security flaw that it can exploit for surveillance purposes, the best thing to do is to disclose that flaw to the company so that it can fix it for future products. That's because vulnerabilities are never just used by law enforcement. Time and time again, security flaws that were created or hoarded by agencies like the FBI and NSA have been used by criminal hackers and foreign governments to carry out attacks.
Even the White House agrees, and has created a program specifically for the government to share vulnerabilities in cases exactly like this. But so far, the FBI is dodging the question, and won't say whether they'll do the right thing here.
The FBI claimed to the court at least 19 times that there was no way they could unlock the iPhone of the San Bernardino shooter without forcing Apple to build a government backdoor into their operating system. They maintained this repeatedly. Under oath. But the consensus among security experts is that this was never true; the FBI misled the court and the public in pursuit of a dangerous precedent.
Now that they've opened the iPhone in question, the mainstream media is already speculating as to how they did it. And it goes without saying that hackers, other governments, and those wishing to exploit this security flaw to do harm to the public are already hard at work trying to figure it out. Worse, the FBI has a terrible track record of protecting it's own data. Just recently they leaked personal information about more than 20,000 FBI agents. They're clearly not capable of keeping this exploit from falling into the wrong hands.
The only responsible thing for the FBI to do to protect all of our safety and security is to disclose the method they used to Apple so they can fix it and make sure it can't be used to carry out future attacks.
Fight for the Future is a group of artists, engineers, activists, and technologists who have been behind the largest online protests in human history, channeling Internet outrage into political power to win public interest victories previously thought to be impossible. We fight for a future where technology liberates -- not oppresses -- us.
(508) 368-3026LATEST NEWS
'Bold Ideas This Country Desperately Needs': Progressive Caucus Unveils Affordability Agenda
"The New Affordability Agenda shows how Democrats can actually make things cheaper for working people by taking on special interests who are ripping people off," said Rep. Greg Casar.
Apr 29, 2026
The Congressional Progressive Caucus on Wednesday unveiled a sweeping affordability agenda aimed at combating a cost-of-living crisis that President Donald Trump and congressional Republicans have supercharged with tariffs, a war of choice in Iran, and deep cuts to safety-net programs.
The CPC's New Affordability Agenda comprises new and previously introduced legislation designed to lower the cost of housing, groceries, childcare, prescription drugs, and more. The caucus presented its slate of policy proposals—which are popular with American voters across the political spectrum—as a positive agenda around which "every single Democrat should be able to unite" heading into the pivotal 2026 midterms and beyond.
“Affordability is not a ‘hoax,'" said CPC Chair Rep. Greg Casar (D-Texas), referring to Trump's efforts to dismiss mounting concerns about cost increases under his administration as consumer sentiment plunges to all-time lows and affordability continues to top Americans' list of concerns.
"It also has to be more than just a slogan,” Casar added. “The New Affordability Agenda shows how Democrats can actually make things cheaper for working people by taking on special interests who are ripping people off. These are the kind of bold, populist ideas Democrats should talk about in 2026 and pass in 2027. We are glad that many of these ideas already have support across the Democratic caucus, and we look forward to working to get them actually passed as soon as possible.”
Endorsed by a broad coalition of labor unions, advocacy groups, and policy experts, the CPC agenda includes 10 planks, each with corresponding legislation.
The first six planks pertain to lowering the costs of essentials: medicine, groceries, housing, utilities, childcare, and gas.
On prescription drugs, for instance, the agenda calls for passage of the Affordable Drug Manufacturing Act, which would establish a federal program to directly manufacture generic medications and offer them to consumers at an affordable price.
On childcare, the CPC is urging passage of a bill led by Rep. Alexandria Ocasio-Cortez (D-NY) and Sen. Elizabeth Warren (D-Mass.) that would ensure "every family in every community has access to high-quality, affordable childcare and early learning opportunities by establishing a network of federally supported, locally administered childcare options."
"In 2026, Democrats cannot politely nibble around the edges when taking on a rigged economic system,” Warren said Wednesday. “Americans want leaders who will fight for bold policies like universal childcare and affordable housing so that we can build an economy for everyone. The New Affordability Agenda is about fighting for the big structural change we need to put working people first."
The CPC agenda also calls for ending AI price gouging, guaranteeing paid vacation to every full-time worker, raising federal overtime pay, and capping super PAC spending on elections.
“At a time when 60% of Americans live paycheck to paycheck and billionaires and large corporations have never had it so good, the Congressional Progressive Caucus is putting forward bold ideas this country desperately needs,” Sen. Bernie Sanders (I-Vt.) said in a statement on Wednesday. “This agenda says that in the richest nation on Earth, we can create an economy that works for every man, woman, and child, and not just a handful of billionaires."
"Yes, we can lower the cost of prescription drugs," said Sanders. "Yes, we can build millions of units of low-income and affordable housing. Yes, we can provide universal, high-quality, affordable childcare in every community. And yes, we can create a vibrant democracy by abolishing super PACs and making sure billionaires can no longer buy elections.”
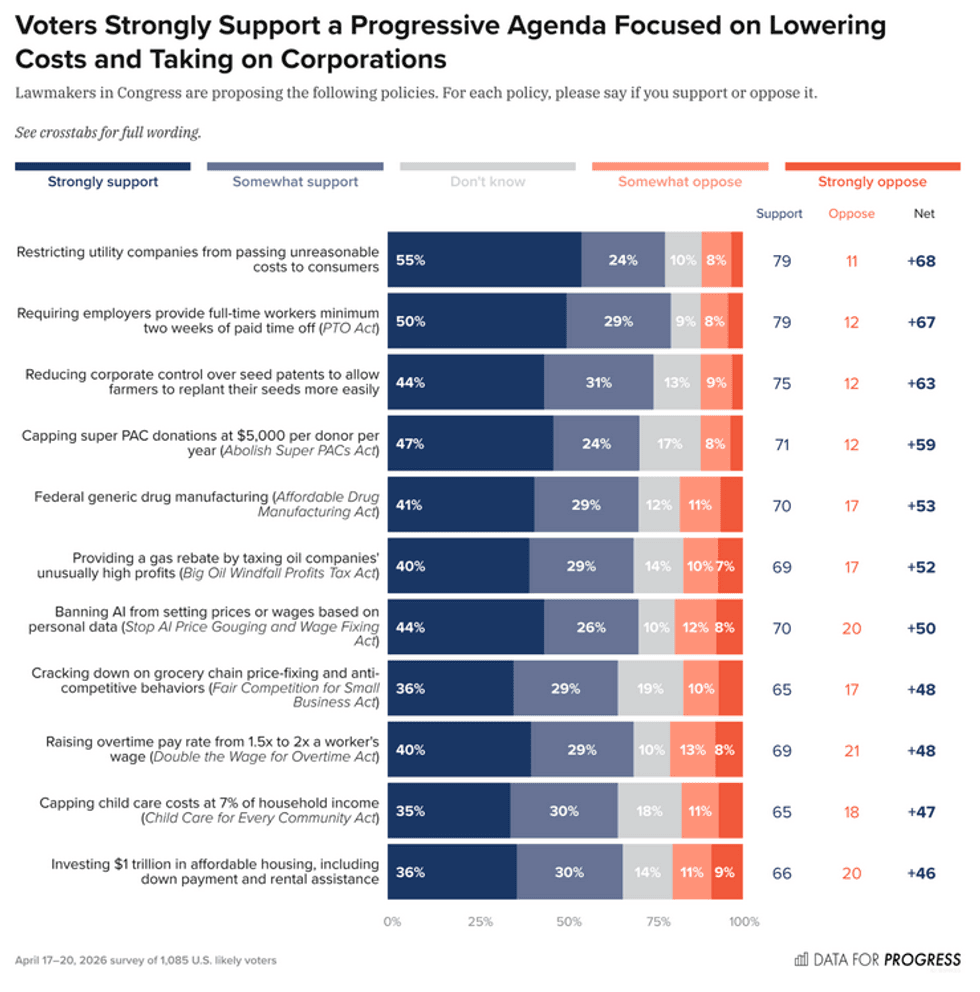
New polling conducted by Data for Progress indicates that all of the individual policies championed by the CPC are broadly popular with the American electorate.
"Every policy tested earns majority support from at least 3 in 5 voters," the polling outfit found. "Requiring two weeks of paid time off for all full-time workers and restricting private utility companies from passing unreasonable costs on to customers are the most popular policies on the list—each earning support from 79% of voters."
Rep. Becca Balint (D-Vt.), who heads the CPC's Ending Corporate Greed Task Force, said Wednesday that Democrats "need to be listening deeply and fighting hard for Americans."
"They have been loud and clear that everything is too damn expensive, and we must respond," said Balint. "This New Affordability Agenda is a strong slate of policy proposals that will help bring down costs. From increasing pay and taking on the corporations that have rigged our economy, to lowering everyday costs on housing, groceries, and childcare, this concrete approach reflects that we understand the scope of the problems and we are ready to take real action."
Keep ReadingShow Less
'Obscene Transfer of Wealth' Continues as Another Oil Giant Posts Massive War-Fueled Profits
"The war enriches shareholders as it impoverishes citizens," said a campaigner with 350.org.
Apr 29, 2026
France-based TotalEnergies on Wednesday became the latest fossil fuel giant to report massive profits juiced by the US-Israeli war on Iran, which has sent global oil prices surging and jacked up costs for consumers.
TotalEnergies announced in its first-quarter earnings report that it would increase returns to shareholders through a higher dividend and stock buybacks after seeing $5.8 billion in profits and $8.6 billion in cash flow during the first three months of 2026. The company attributed its profit growth to its "ability to capture price upside," corporate-speak for cashing in as consumers face rising energy costs.
“While families watch their bills skyrocket, TotalEnergies posts some of its best financial results without even paying its fair share of taxes," said Fanny Petitbon, France country manager at the environmental group 350.org. "We are witnessing an obscene transfer of wealth: The war enriches shareholders as it impoverishes citizens."
"We demand that France stop yielding to oil lobbyists and introduce, without delay, a permanent and ambitious tax on fossil fuel profits," Petitbon added. "Every day of inaction is a deliberate political choice in favor of shareholders and against citizens.”
TotalEnergies' report came a day after the British oil giant BP reported that its profits more than doubled compared to the first quarter of last year.
In an analysis released over the weekend, Oxfam projected that six of the world's largest fossil fuel companies—including BP and TotalEnergies—will rake in $2,967 in profits per second this year, an increase of roughly $37 million per day compared to last year.
"Families around the world continue to be pushed into energy poverty as geopolitical instability, the impacts of escalating violence in the Middle East that has already taken many lives, and the sharp increase in the wealth of the super-rich in contrast to everyone else are leaving ordinary people struggling to make ends meet," said Oxfam.
350.org warned earlier this week that energy market disruptions caused by the US-Israeli war on Iran could hit households, businesses, and governments around the world with more than $1 trillion in extra costs.
“It is a staggering injustice that fossil fuel corporations are once again posting record-breaking profits while families struggle to keep the lights on," said Rukiya Khamis, 350.org's East Africa country manager. "Right now, power is concentrated in the hands of those who thrive on crisis and scarcity."
"It’s time to end our forced dependence on fossil fuels, tax the profiteers who benefit from our hardship, and redirect that wealth into building a fair, clean energy system," Khamis said. "We aren’t just asking for a lower bill; we are demanding a system that values human dignity over corporate greed."
Keep ReadingShow Less
Fetterman Helps GOP Senators Sink Democrat Effort to Block Trump War on Cuba
"The last thing working Americans need right now is another war," said the Senate's top Democrat.
Apr 28, 2026
The US Senate on Tuesday defeated a Democrat-led bid to stop President Donald Trump from following through on his threat to wage war on Cuba, whose long-suffering people are reeling from the American administration's tightened economic stranglehold.
Upper chamber lawmakers voted 51-47 on a procedural motion to block further debate Sen. Tim Kaine's (D-Va.) SJ Res. 124, "a joint resolution to direct the removal of United States armed forces from hostilities within or against the republic of Cuba that have not been authorized by Congress."
Republican Sens. Susan Collins of Maine and Rand Paul of Kentucky voted to advance the resolution, while John Fetterman of Pennsylvania joined his GOP colleagues in voting to sink the measure.
The vote effectively sidelines the measure, one of many failed attempts to curb Trump's ability to wage war on countries including Iran and Venezuela, as well as rein in his high seas boat bombing spree.
“The American people are not asking for another war," Sen. Ruben Gallego (D-Ariz.)—one of SJ Res. 124's dozen co-sponsors—said following Tuesday's vote. "They want us focused on building housing in Arizona, not bombing housing in Havana. They want us to lower the cost of healthcare not condemn a generation of veterans to a lifetime of hospital visits. They want us to make their lives more affordable, not spend their tax dollars on unnecessary wars."
Kaine called the GOP move "purely a regime change effort."
"Why do they want it? You'll have to ask them," he added. "What we're doing with respect to Cuba, if somebody was doing it to us, we would consider it an act of war. But because they don't pose a security threat to the United States, it's clearly an effort to change the regime."
Senate Minority Leader Chuck Schumer (D-NY), who also co-sponsored the resolution, said, "The last thing working Americans need right now is another war—let alone one that’s 90 miles south of the US."
Resolution co-sponsor Sen. Angela Alsobrooks (D-Md.) said on Bluesky after the vote, "A conflict with Cuba would cost hardworking Americans billions of dollars, deepen the humanitarian crisis in Cuba, and put American service members in harm’s way."
"The Constitution is clear: Only Congress has the authority to declare war," Alsobrooks added.
Trump has attacked seven countries since returning to office and 10 since the start of his first term—more than any other president.
The situation in Cuba is dire, as a result of both the 65-year US economic chokehold on the island and mismanaged central planning by its socialist rulers.
Trump has been ramping up military threats and economic pressure on Cuba, whose people were already suffering from generations of US sanctions. His administration's tightened embargo has severely restricted fuel imports, worsening an energy emergency in which blackouts have become the norm, threatening the lives of vulnerable Cubans—especially sick people and children.
The US president said that “we may stop by Cuba after we’re finished" with the illegal US-Israeli war of choice on Iran that’s killed thousands of people, including hundreds of children. Trump has also said that he believes he’ll “be having the honor of taking Cuba."
The United States already took Cuba once, during an 1898 war waged against Spain under highly dubious pretenses that ended with the US also acquiring Puerto Rico, the Philippines, and Guam—with Hawaii also annexed that year under the guise of security.
American presidents have been trying to force out Cuba's socialist government since shortly after the revolution that overthrew a US-backed dictatorship in 1959. US efforts have included carrying out or backing an armed invasion, terrorist attacks, assassination attempts, and other acts of aggression.
Cuba commits no such acts against the United States or anyone else, yet Trump added the country to the US State Sponsors of Terrorism list.
Following Tuesday's vote, Sen. Ed Markey (D-Mass.) said that "Trump should learn the law of holes: If you find yourself in one, stop digging."
"Instead of threatening that ‘Cuba is next,’ President Trump should remove his blockade against Cuba, which has devastated Havana’s economy and healthcare system, and has created a deepening humanitarian crisis," Markey added.
The United Nations General Assembly has overwhelmingly condemned the blockade 33 times since 1992.
“With its catastrophic Iran war of choice, the Trump administration has lost all credibility on issues of war and peace," Markey asserted. "The American people do not want yet another endless war that will only costs more lives and more taxpayer dollars, and undermine US security.”
Progressive International co-general coordinator David Adler warned Tuesday that "Trump is preparing military action against Cuba," calling the Senate vote possibly "the last chance for US Congress to stop it."
Keep ReadingShow Less
Most Popular