

SUBSCRIBE TO OUR FREE NEWSLETTER
Daily news & progressive opinion—funded by the people, not the corporations—delivered straight to your inbox.
5
#000000
#FFFFFF
To donate by check, phone, or other method, see our More Ways to Give page.


Daily news & progressive opinion—funded by the people, not the corporations—delivered straight to your inbox.
"Our ability to pull bits out of random places of the Internet, bring them back to the mother-base to evaluate and build intelligence off of is just plain awesome!" --NSA employee
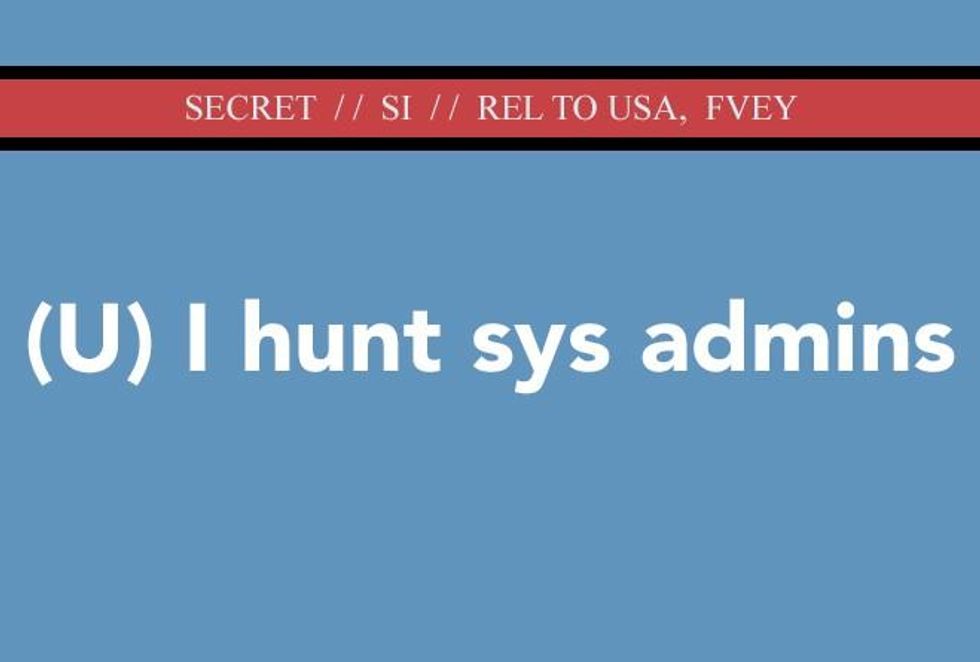
Though those targeted were not suspected of any wrong doing whatsoever, internal NSA documents provided by NSA whistleblower Edward Snowden show that these people, called "sys admins" for short, had their email and Facebook accounts tracked as the government hackers tried to access their "network maps, customer lists, [and] business correspondence."
The overall effort by the NSA relates to previously reported programs based on Snowden documents that show efforts by the US surveillance agency and their British counterparts at the GCHQ to gain direct access to "foreign network routers" and other digital systems without the companies or governments who control those networks knowing. "Who better to target than the person that already has the 'keys to the kingdom'?" asks one NSA-employed hacker in a post cited by The Intercept.
Strikingly, according to the reporting by journalists Ryan Gallagher and Peter Maass, these internal NSA "posts" were written by an individual NSA employee thought to be a contract "network specialist" with a highly "boastful and casual tone," describing how bits of personal data--like "pictures of cats in funny poses with amusing captions"--could also be harvested alongside information related to the professional work of the targeted sys admin. The posts are full of "hacker jargon (pwn, skillz, zomg, internetz)" and "punctuated with expressions of mischief" such as "Current mood: devious." Another reads: "Current mood: scheming."
Gallagher and Maass report:
It is unclear how precise the NSA's hacking attacks are or how the agency ensures that it excludes Americans from the intrusions. The author explains in one post that the NSA scours the Internet to find people it deems "probable" administrators, suggesting a lack of certainty in the process and implying that the wrong person could be targeted. It is illegal for the NSA to deliberately target Americans for surveillance without explicit prior authorization. But the employee's posts make no mention of any measures that might be taken to prevent hacking the computers of Americans who work as sys admins for foreign networks. Without such measures, Americans who work on such networks could potentially fall victim to an NSA infiltration attempt.
Here's how it works:
The first step, according to the posts, is to collect IP addresses that are believed to be linked to a network's sys admin. An IP address is a series of numbers allocated to every computer that connects to the Internet. Using this identifier, the NSA can then run an IP address through the vast amount of signals intelligence data, or SIGINT, that it collects every day, trying to match the IP address to personal accounts.
"What we'd really like is a personal webmail or Facebook account to target," one of the posts explains, presumably because, whereas IP addresses can be shared by multiple people, "alternative selectors" like a webmail or Facebook account can be linked to a particular target. You can "dumpster-dive for alternate selectors in the big SIGINT trash can" the author suggests. Or "pull out your wicked Google-fu" (slang for efficient Googling) to search for any "official and non-official e-mails" that the targets may have posted online.
Once the agency believes it has identified a sys admin's personal accounts, according to the posts, it can target them with its so-called QUANTUM hacking techniques. The Snowden files reveal that the QUANTUM methods have been used to secretly inject surveillance malware into a Facebook page by sending malicious NSA data packets that appear to originate from a genuine Facebook server. This method tricks a target's computer into accepting the malicious packets, allowing the NSA to infect the targeted computer with a malware "implant" and gain unfettered access to the data stored on its hard drive.
"Just pull those selectors, queue them up for QUANTUM, and proceed with the pwnage," the author of the posts writes. ("Pwnage," short for "pure ownage," is gamer-speak for defeating opponents.) The author adds, triumphantly, "Yay! /throws confetti in the air."
In a final detail worth noting, The Intercept describe how the NSA posts contained in the slides reveal the internal debate at the agency over the sheer volume of data being collected by their various surveillance techniques. Whereas some agents criticized the poor infrastructure and its inability to handle so much data from around the globe, other employees celebrated what has become known as the NSA's "collect it all approach" to the world of online surveillance.
"Our ability to pull bits out of random places of the Internet, bring them back to the mother-base to evaluate and build intelligence off of is just plain awesome!" the author writes. "One of the coolest things about it is how much data we have at our fingertips."
____________________________________
Dear Common Dreams reader, The U.S. is on a fast track to authoritarianism like nothing I've ever seen. Meanwhile, corporate news outlets are utterly capitulating to Trump, twisting their coverage to avoid drawing his ire while lining up to stuff cash in his pockets. That's why I believe that Common Dreams is doing the best and most consequential reporting that we've ever done. Our small but mighty team is a progressive reporting powerhouse, covering the news every day that the corporate media never will. Our mission has always been simple: To inform. To inspire. And to ignite change for the common good. Now here's the key piece that I want all our readers to understand: None of this would be possible without your financial support. That's not just some fundraising cliche. It's the absolute and literal truth. We don't accept corporate advertising and never will. We don't have a paywall because we don't think people should be blocked from critical news based on their ability to pay. Everything we do is funded by the donations of readers like you. Will you donate now to help power the nonprofit, independent reporting of Common Dreams? Thank you for being a vital member of our community. Together, we can keep independent journalism alive when it’s needed most. - Craig Brown, Co-founder |
"Our ability to pull bits out of random places of the Internet, bring them back to the mother-base to evaluate and build intelligence off of is just plain awesome!" --NSA employee
Though those targeted were not suspected of any wrong doing whatsoever, internal NSA documents provided by NSA whistleblower Edward Snowden show that these people, called "sys admins" for short, had their email and Facebook accounts tracked as the government hackers tried to access their "network maps, customer lists, [and] business correspondence."
The overall effort by the NSA relates to previously reported programs based on Snowden documents that show efforts by the US surveillance agency and their British counterparts at the GCHQ to gain direct access to "foreign network routers" and other digital systems without the companies or governments who control those networks knowing. "Who better to target than the person that already has the 'keys to the kingdom'?" asks one NSA-employed hacker in a post cited by The Intercept.
Strikingly, according to the reporting by journalists Ryan Gallagher and Peter Maass, these internal NSA "posts" were written by an individual NSA employee thought to be a contract "network specialist" with a highly "boastful and casual tone," describing how bits of personal data--like "pictures of cats in funny poses with amusing captions"--could also be harvested alongside information related to the professional work of the targeted sys admin. The posts are full of "hacker jargon (pwn, skillz, zomg, internetz)" and "punctuated with expressions of mischief" such as "Current mood: devious." Another reads: "Current mood: scheming."
Gallagher and Maass report:
It is unclear how precise the NSA's hacking attacks are or how the agency ensures that it excludes Americans from the intrusions. The author explains in one post that the NSA scours the Internet to find people it deems "probable" administrators, suggesting a lack of certainty in the process and implying that the wrong person could be targeted. It is illegal for the NSA to deliberately target Americans for surveillance without explicit prior authorization. But the employee's posts make no mention of any measures that might be taken to prevent hacking the computers of Americans who work as sys admins for foreign networks. Without such measures, Americans who work on such networks could potentially fall victim to an NSA infiltration attempt.
Here's how it works:
The first step, according to the posts, is to collect IP addresses that are believed to be linked to a network's sys admin. An IP address is a series of numbers allocated to every computer that connects to the Internet. Using this identifier, the NSA can then run an IP address through the vast amount of signals intelligence data, or SIGINT, that it collects every day, trying to match the IP address to personal accounts.
"What we'd really like is a personal webmail or Facebook account to target," one of the posts explains, presumably because, whereas IP addresses can be shared by multiple people, "alternative selectors" like a webmail or Facebook account can be linked to a particular target. You can "dumpster-dive for alternate selectors in the big SIGINT trash can" the author suggests. Or "pull out your wicked Google-fu" (slang for efficient Googling) to search for any "official and non-official e-mails" that the targets may have posted online.
Once the agency believes it has identified a sys admin's personal accounts, according to the posts, it can target them with its so-called QUANTUM hacking techniques. The Snowden files reveal that the QUANTUM methods have been used to secretly inject surveillance malware into a Facebook page by sending malicious NSA data packets that appear to originate from a genuine Facebook server. This method tricks a target's computer into accepting the malicious packets, allowing the NSA to infect the targeted computer with a malware "implant" and gain unfettered access to the data stored on its hard drive.
"Just pull those selectors, queue them up for QUANTUM, and proceed with the pwnage," the author of the posts writes. ("Pwnage," short for "pure ownage," is gamer-speak for defeating opponents.) The author adds, triumphantly, "Yay! /throws confetti in the air."
In a final detail worth noting, The Intercept describe how the NSA posts contained in the slides reveal the internal debate at the agency over the sheer volume of data being collected by their various surveillance techniques. Whereas some agents criticized the poor infrastructure and its inability to handle so much data from around the globe, other employees celebrated what has become known as the NSA's "collect it all approach" to the world of online surveillance.
"Our ability to pull bits out of random places of the Internet, bring them back to the mother-base to evaluate and build intelligence off of is just plain awesome!" the author writes. "One of the coolest things about it is how much data we have at our fingertips."
____________________________________
"Our ability to pull bits out of random places of the Internet, bring them back to the mother-base to evaluate and build intelligence off of is just plain awesome!" --NSA employee
Though those targeted were not suspected of any wrong doing whatsoever, internal NSA documents provided by NSA whistleblower Edward Snowden show that these people, called "sys admins" for short, had their email and Facebook accounts tracked as the government hackers tried to access their "network maps, customer lists, [and] business correspondence."
The overall effort by the NSA relates to previously reported programs based on Snowden documents that show efforts by the US surveillance agency and their British counterparts at the GCHQ to gain direct access to "foreign network routers" and other digital systems without the companies or governments who control those networks knowing. "Who better to target than the person that already has the 'keys to the kingdom'?" asks one NSA-employed hacker in a post cited by The Intercept.
Strikingly, according to the reporting by journalists Ryan Gallagher and Peter Maass, these internal NSA "posts" were written by an individual NSA employee thought to be a contract "network specialist" with a highly "boastful and casual tone," describing how bits of personal data--like "pictures of cats in funny poses with amusing captions"--could also be harvested alongside information related to the professional work of the targeted sys admin. The posts are full of "hacker jargon (pwn, skillz, zomg, internetz)" and "punctuated with expressions of mischief" such as "Current mood: devious." Another reads: "Current mood: scheming."
Gallagher and Maass report:
It is unclear how precise the NSA's hacking attacks are or how the agency ensures that it excludes Americans from the intrusions. The author explains in one post that the NSA scours the Internet to find people it deems "probable" administrators, suggesting a lack of certainty in the process and implying that the wrong person could be targeted. It is illegal for the NSA to deliberately target Americans for surveillance without explicit prior authorization. But the employee's posts make no mention of any measures that might be taken to prevent hacking the computers of Americans who work as sys admins for foreign networks. Without such measures, Americans who work on such networks could potentially fall victim to an NSA infiltration attempt.
Here's how it works:
The first step, according to the posts, is to collect IP addresses that are believed to be linked to a network's sys admin. An IP address is a series of numbers allocated to every computer that connects to the Internet. Using this identifier, the NSA can then run an IP address through the vast amount of signals intelligence data, or SIGINT, that it collects every day, trying to match the IP address to personal accounts.
"What we'd really like is a personal webmail or Facebook account to target," one of the posts explains, presumably because, whereas IP addresses can be shared by multiple people, "alternative selectors" like a webmail or Facebook account can be linked to a particular target. You can "dumpster-dive for alternate selectors in the big SIGINT trash can" the author suggests. Or "pull out your wicked Google-fu" (slang for efficient Googling) to search for any "official and non-official e-mails" that the targets may have posted online.
Once the agency believes it has identified a sys admin's personal accounts, according to the posts, it can target them with its so-called QUANTUM hacking techniques. The Snowden files reveal that the QUANTUM methods have been used to secretly inject surveillance malware into a Facebook page by sending malicious NSA data packets that appear to originate from a genuine Facebook server. This method tricks a target's computer into accepting the malicious packets, allowing the NSA to infect the targeted computer with a malware "implant" and gain unfettered access to the data stored on its hard drive.
"Just pull those selectors, queue them up for QUANTUM, and proceed with the pwnage," the author of the posts writes. ("Pwnage," short for "pure ownage," is gamer-speak for defeating opponents.) The author adds, triumphantly, "Yay! /throws confetti in the air."
In a final detail worth noting, The Intercept describe how the NSA posts contained in the slides reveal the internal debate at the agency over the sheer volume of data being collected by their various surveillance techniques. Whereas some agents criticized the poor infrastructure and its inability to handle so much data from around the globe, other employees celebrated what has become known as the NSA's "collect it all approach" to the world of online surveillance.
"Our ability to pull bits out of random places of the Internet, bring them back to the mother-base to evaluate and build intelligence off of is just plain awesome!" the author writes. "One of the coolest things about it is how much data we have at our fingertips."
____________________________________